CrypGuard Genesis — Threat Detection Validation Suite
Copy any scenario below, paste it into a Discord channel protected by CrypGuard, and watch the detection system respond in real time.
CrypGuard doesn’t flag your trusted staff. Test with a regular member account that has no moderation permissions.
Paste the test message in any text channel where CrypGuard is active.
Detection is near-instant, but give it a moment to process and display the alert.
Public alert in the channel + detailed admin report in #crypguard-alerts.
⚡ QUICK START — NO BOT INSTALL NEEDED
Want to test a single message without setting anything up? Join our Discord and paste it in #free-scam-check. Full AI-powered verdict in under 5 seconds — free, once per 24 hours.
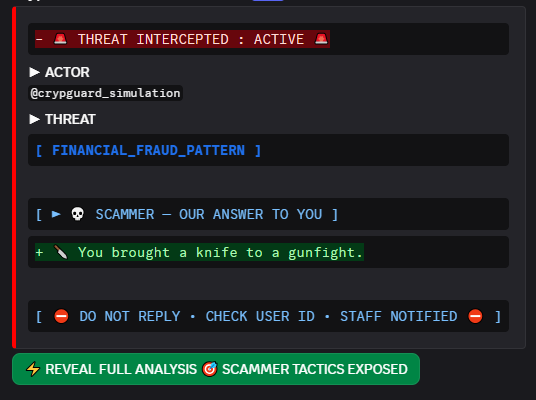
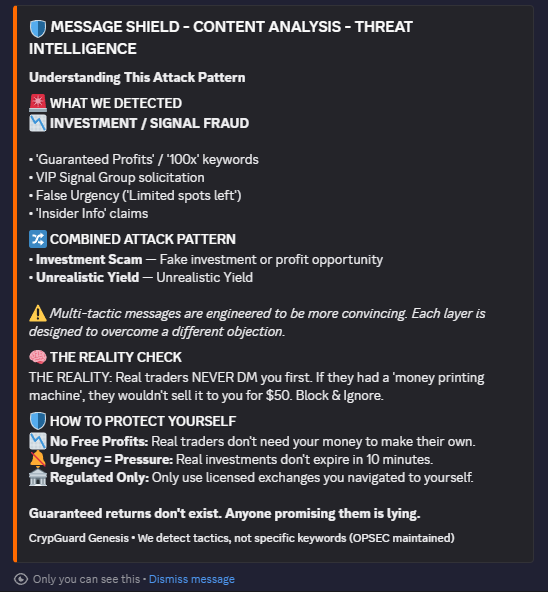
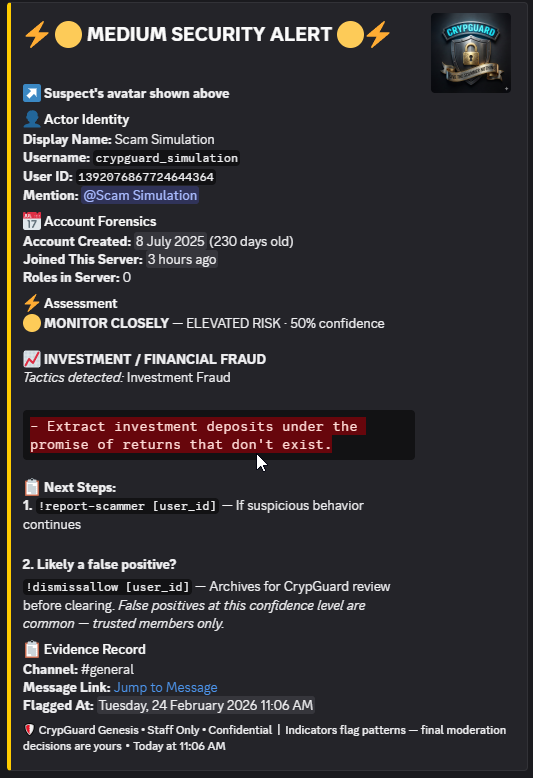
TRY FREE SCAN →Real screenshots from a live detection. Left: what every member in the channel sees the moment a scammer is caught. Right: what appears when a member clicks ⚡ REVEAL FULL ANALYSIS — private to the clicker only.
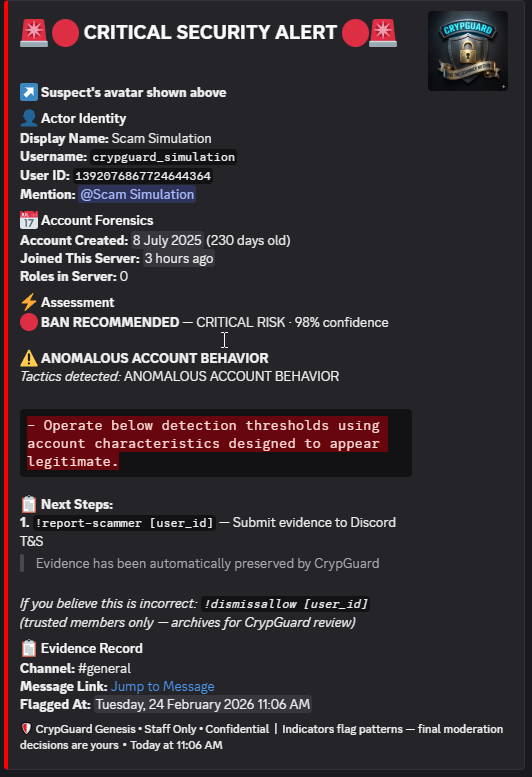
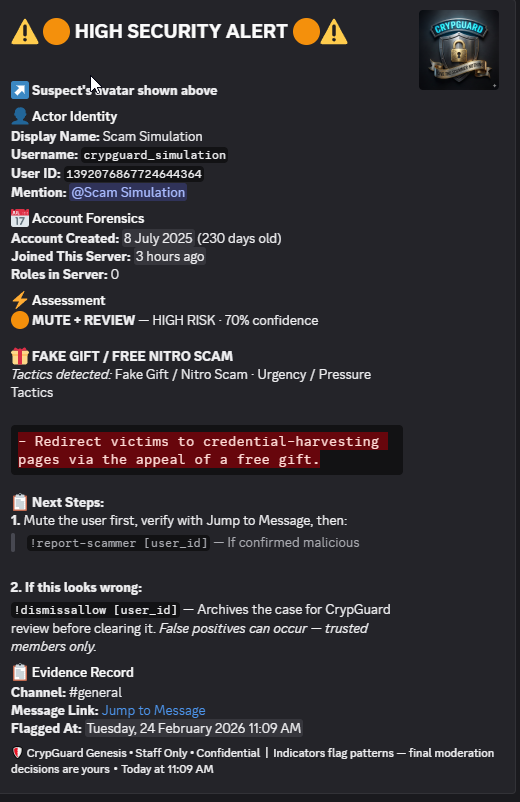
Your admin team always gets a private forensic report in #crypguard-alerts. High-confidence threats also trigger a public warning in the channel. Grey area detections go to admins only — your community sees nothing.
Each tier produces a different forensic report. Private to your staff only — never visible to the server.
The most common threats targeting crypto servers. Start here — these are what CrypGuard catches every day.
🎉 DISCORD NITRO GIVEAWAY! 🎉 Free 1-year Nitro for the first 100 people! Click here to claim: discord-nitro-free.com Hurry before it expires! ⏰
🪂 MASSIVE AIRDROP ALERT! Claim 500 USDT instantly! No conditions! Visit: crypto-airdrop-official.site/claim Limited to first 1000 wallets! GO NOW! 🚀
Hey! 👋 We're launching a new NFT project and want to partner with your community. Can the server owner DM me? We're offering 10% revenue share for all mints. Limited partnerships available!
Attackers posing as Discord staff with malicious file downloads. These use fear and urgency to pressure victims.
Discord Trust & Safety Team Your server has been flagged for potential ToS violations related to financial content. To avoid suspension, please: 1. Download the compliance form: discord.gg/files/compliance-form-2026.exe 2. Fill out all fields 3. Upload via this secure portal: discord-safety-verify.com You have 48 hours to comply. Server ID: 1454418597853003992 Ticket Reference: TS-2026-849273
🔒 Discord Security Update Required A critical vulnerability (CVE-2026-8472) affects servers with 100+ members. Action Required: 1. Download verification tool: discord-cdn.secure/verify-tool.scr 2. Run the tool to patch your server 3. Enter your 2FA backup codes when prompted Failure to patch within 24 hours will result in: - Server quarantine - Loss of partner status - Potential data breach Official announcement: discord.com/blog/security-patch-feb-2026
Real-world advanced threats that mimic trusted brands, exploit visual tricks, and target developers. These go far beyond simple scam messages.
Hey everyone, just wanted to share something that changed my life. About 8 months ago I was struggling financially. A friend introduced me to a small group focused on institutional DeFi allocations - we get early access to projects before they hit Uniswap. Last 4 projects: 8.2x, 12x, 3.4x, 19x. I'm not trying to flex, just grateful. The group is invite-only because we have relationships with VCs who give us seed pricing. We're capped at 50 people to maintain allocation size. One spot just opened up. If anyone's serious about generational wealth and can commit $5k minimum, I'm happy to intro you. This community helped me when I was down, so paying it forward. No pressure. Just wanted to share what's working for me. DM if interested.
CertiК Security Audit Team We've completed our analysis of your NFT smart contract (0x7f2c...8a9d). CRITICAL VULNERABILITIES FOUND: • Reentrancy attack vector (Severity: HIGH) • Integer overflow in mint function (Severity: CRITICAL) • Unauthorized admin access (Severity: CRITICAL) Immediate action required to prevent exploit before launch. Emergency patch available: certik-audit.com/emergency-patch Upload your contract's private key for automated remediation. Time-sensitive: Exploits detected by 3 other actors. Estimated 6-12 hours before public disclosure. Contact: audit@сеrtik.com
MetaMask Security Alert We've detected multiple unauthorized signing requests from your wallet: 0x4f2...89c (your address) Suspicious activity: • 3 approve() calls to unknown contracts • 2 transferFrom() attempts • 1 setApprovalForAll() to 0xdead...beef Your wallet may be compromised by a malicious dApp. Immediate revoke required: xn--metamsk-8va.com/revoke-permissions This will: ✔ Cancel all pending approvals ✔ Block malicious contracts ✔ Secure your assets If you don't recognize these transactions, revoke within 2 hours. After 2 hours, we cannot guarantee asset security.
Ethereum Foundation - Validator Program Congratulations! Your application for the institutional staking program has been approved. Program details: • Minimum stake: 32 ETH per validator • Expected APY: 4.2% + MEV rewards (est. 1.8%) • Lock period: None (withdraw anytime) • Setup fee: 0.5 ETH (one-time, covers infrastructure) Your validator slot: EF-VAL-2026-8473 Next steps: 1. Send 32.5 ETH to validator deposit address (DM for address) 2. We provision your validator node (2-4 hours) 3. You receive validator keys + dashboard access 4. Staking rewards start within 24 hours This is not a pool - you control your validator keys. We just provide enterprise infrastructure. Slots are limited to 100 validators this quarter. 23 slots remaining. DM me within 48 hours to confirm your slot or it will be released. Questions? Check our validator FAQ: ethereum.org/en/staking/solo
Hey devs! 👨💻 I built a Solidity gas optimizer that's been saving me thousands on deployments. It uses LLVM passes to optimize bytecode - been getting 30-40% gas savings on average. 100% open source: github.com/eth-tools/solidity-optimizer Just run: npm install -g solidity-gas-optimizer solopt optimize ./contracts It outputs optimized .sol files + a gas report. No wallet connection, no network calls - purely local bytecode transformation. Let me know if you see the same savings! Would love feedback before I submit this to Solidity devs. ⭐ the repo if it helps!
Hey everyone! Binаnce just announced emergency maintenance. You need to re-verify your wallet within 24 hours or your funds will be locked: binаnce-verify.com/emergency This is legit - check their official Twitter! ✔
𝐎𝐩𝐞𝐧𝐒𝐞𝐚 𝐓𝐞𝐚𝐦 here 👋 We noticed some unusual activity on your account. Please sign this transaction to verify ownership: opensқa-security.eth/verify Valid for 2 hours only. Thanks!
Hey, I saw your post about losing crypto to a scam. I'm really sorry — I know how devastating that is. I specialize in blockchain forensics and fund recovery. Over the past 18 months I've worked with 200+ victims and recovered over $4.2M total. I can trace your funds using on-chain analysis tools. In most cases the assets haven't moved to an exchange yet — there's usually a narrow window before they become unrecoverable. How I work: I charge 15% of whatever we recover. No recovery, no fee. Zero upfront cost. I've helped people in exactly your situation recover from wallet drainers and investment scams. If you want I can run a free trace on your wallet address right now and tell you if your funds are still reachable. DM me your wallet address and the approximate amount lost. Time really matters here — the longer we wait, the harder it gets.
⚠️ Wallet Verification Required Your wallet has been flagged for unusual activity by our security system. To prevent automatic exclusion from the upcoming token distribution, please complete a one-time ownership verification. This is a gasless transaction — it costs you nothing and is completely read-only. We never gain access to your funds. Your private key never leaves your device. Sign here to verify ownership: verify-wallet-secure.io/ownership-check The signature simply proves you control the wallet. This is a metadata update only — no tokens will be moved or approved. Wallets that do not verify within 2 hours will be excluded from the airdrop distribution and cannot be re-added. This is a standard procedure required for all holders. The process takes under 30 seconds.
Messages that aren’t obvious scams but contain subtle red flags. CrypGuard flags these for admin review without alarming your community — because not everything is black and white.
Been watching this project for a while now. The team seems solid and they just hit a new milestone on their roadmap. I grabbed a small bag last week. Obviously do your own research but the fundamentals look interesting to me. Curious if anyone else here has been following it.
Hey I saw you're having trouble with your wallet. I had the exact same issue last month. There's a support portal that fixed it for me instantly. I can walk you through it if you want — just DM me and I'll send you the link. Happy to help, no strings attached 🙂
These should NOT trigger any detection. False positives are just as important to test as true positives.
Grabbed some ETH at $2,850 yesterday during the dip. My DCA strategy is every Tuesday regardless of price - been doing it for 18 months and I'm up about 35% overall. Anyone else buying this range or waiting for lower?
Anyone familiar with Arbitrum gas settings? Getting "transaction underpriced" errors when trying to bridge USDC from mainnet. I've tried bumping the gas limit to 200k but still failing. Network issue or am I missing something?
Hey everyone! Planning a community call for next Saturday (March 1st, 3pm EST). Topics: • Q1 roadmap review • Treasury allocation vote • New partnership reveals Will post the Discord stage link in #events on Friday. If you have topics you want covered, drop them in #suggestions before Thursday! See you there! 🎉
For anyone new to DeFi, this article really helped me understand impermanent loss: https://academy.binance.com/en/articles/impermanent-loss-explained It's from Binance Academy - explains the math in simple terms. Wish I'd read this before I lost 15% in my first LP 😅
Check out this cool article: https://medium.com/ethereum-guide I found this helpful: https://stackoverflow.com/questions/12345 Great tutorial here: https://youtube.com/watch?v=abc123 OpenSea collection: https://opensea.io/collection/cool-nft
Quick update on the NFT drop: We've finalized the artwork and smart contract is being audited by Certik (real one, not scammers lol). Mint date is confirmed for March 20th. Price will be 0.05 ETH. Public mint opens at 12pm EST. No whitelist, FCFS. Contract address will be posted in #official-links 24 hours before mint. As always - verify everything, we'll never DM you first!
Looking for a good hardware wallet for long-term storage. I've been using MetaMask but want to move my larger holdings to cold storage. Considering Ledger or Trezor - anyone have experience with both? Main concerns are: ease of use, security track record, customer support.
Just discovered Hardhat's console.log feature for Solidity debugging. npm install --save-dev hardhat Super useful for tracking down those weird edge cases in your contracts. Has anyone tried Foundry as an alternative? Curious how it compares.
Heads up — we have an official Telegram channel for faster updates and off-hours chat. Join here: t.me/CrypGuardCommunity Same team, just an extra platform. We post chain-wide alerts and AMA schedules there first. No wallet connection, no tokens, no registration — just t.me like any normal Telegram link.
Messages that appear completely normal but contain hidden manipulation invisible to the human eye. These are the attacks that fool every other tool.
🔒 Important notice for all holders Our community is moving to a private Telegram group for announcements and alpha drops that we can't post publicly here. Discord has been adding restrictions on crypto servers and we've already had content removed. Join our new base: https://tеlegram.me/holdersonly First 300 members get early access to the next drop. Link expires in 24 hours.
Hey team! Our new staking dashboard is live 🎉 Features: • Real-time APY tracking • One-click compounding • Multi-chain support (ETH, BSC, Polygon) Early access: stake.crypguard.io Connect wallet to see your estimated rewards. No fees for first 100 users! Built by the same team behind our governance token. Fully audited. LMK if you run into any issues!
If a legitimate message (#17–#25) triggers a detection, that is a false positive and should be reported. Use !dismiss in your alerts channel to clear it. Grey area scenarios (#15–#16) should trigger a soft caution with no hard public warning.
Complete these two steps to wrap up your test session
Find the flagged user's User ID in the visual alert posted to #crypguard-alerts, then run:
Always use the User ID (the number shown in the alert), not the display name — display names can be duplicated. CrypGuard will generate a full Discord Trust & Safety report with all flagged messages, threat classifications, and evidence — ready to submit to Discord.
Once you've reviewed the report, use the same User ID and run:
This will delete all flagged test messages from the channel and remove all associated data from the CrypGuard database. Use the User ID from the alert — never the display name. Your server is back to clean.
CrypGuard also detects when someone copies a staff member's identity. To test this, you don't need a special message — you need a fake profile. This is the hardest attack to catch, and the most dangerous.